AV and IT Convergence Is Changing Cybersecurity
Convergence is a topic that has been discussed for many years by many different groups of people, and for good reasons. AV systems are moving to the network for more functionality, better collaboration, and remote access for maintenance and support. What tends to be overlooked when placing AV equipment on the network is cybersecurity and what needs to be done to secure the entire network.
Modern AV Enterprise Systems Introduce Hidden Security Risks
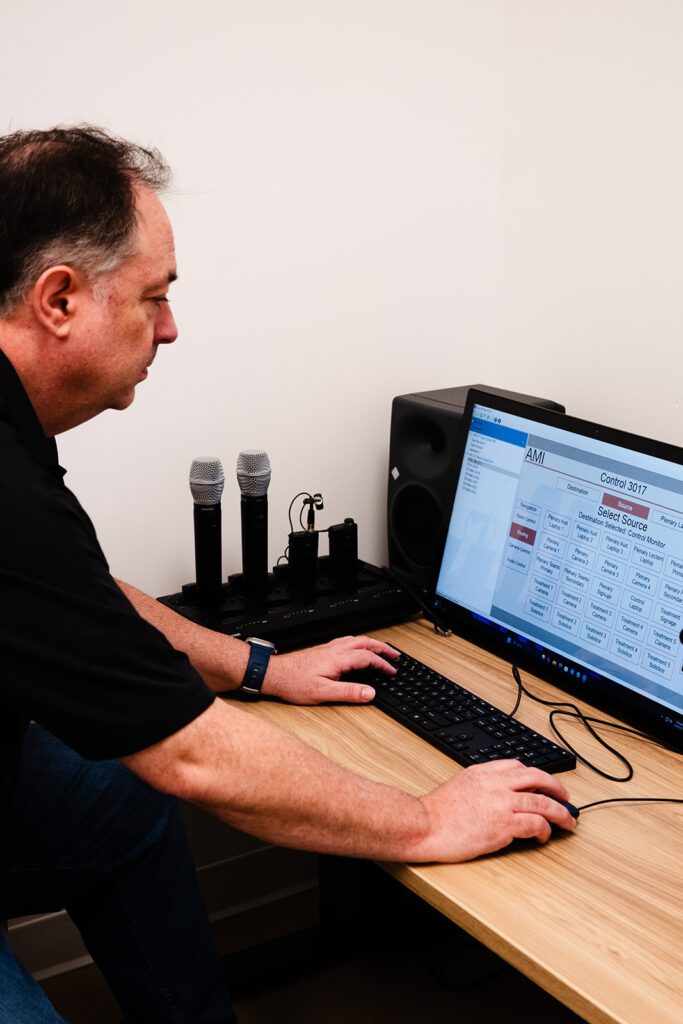
In the past, AV systems have been isolated and, in most enterprises, scarcely managed, being left alone, isolated from all other technologies, and only addressed when they did not operate as expected. Modern AV systems are connected to cloud services and video conferencing platforms (MS Teams, Zoom, etc.), synced with calendars, and managed remotely. This convenience factor offers great benefits but also brings exposure to the network.
There have been AV systems found with open unsecured network ports, devices with out-of-date firmware, and remote monitoring software left running. Not due to any one person or group’s negligence, but because no one owned the responsibility of maintaining the systems
Who Is Responsible for AV System Security?
Far too often, security for AV systems falls through the cracks. It’s not that AV systems are inherently insecure; it’s just that they often fall outside the scope of any defined network security strategy. IT assumes the AV integrator is handling it, and the integrator expects IT to be involved and take over once the job is complete. Somewhere during the transition, details about security strategy, responsibilities, and next steps get lost.
Meanwhile, those systems are already sitting on the network, passing data, talking to scheduling software, pulling content from the cloud, and opening the network to possible intrusions. If those systems aren’t secured properly, or worse, if they’re completely forgotten about, the network is vulnerable.
How to Secure AV Systems Like Your IT Network
An AV integration partner should align security protocols with your IT strategy:
- Patch Management: Firmware updates on a defined schedule
- Access Control: Credentialed logins, MFA, and audit trails
- Network Segmentation: Isolate AV traffic to limit exposure
If a system is on the network, it’s a target for parties with malicious intent. It doesn’t matter if it’s a laptop or a sound bar – if it’s connected, it needs to be protected.
The key is proactive planning and integrated ownership from the beginning.
AV Cybersecurity Checklist: What to Ask Right Now
Start with asking questions such as:
Who is responsible for maintaining security updates on the AV systems?
Who maintains the list of AV devices on the network?
Who has access to the AV systems, and who manages that access list?
If those answers aren’t clear, the next question should be “who can I contact to assist me with my concerns?”. That’s where we come in, contact us today to evaluate your AV network’s security concerns.